Manage Device Deployment
The Deployment Key feature provides an effective way to manage device registration within organizations while mitigating unauthorized access. This feature introduces the concept of a deployment key that can be activated, deactivated, and revoked. By utilizing deployment keys, administrators gain control over the credentials used by devices during registration for Secure Access protection. A deployment key is a field in the Android configuration file (mobileconfigAndroid.txt), which is used when registering devices to your organization's network. This feature ensures that only authorized devices are enrolled by requiring an active deployment key for registration.
|
|
Devices that are deleted from the dashboard will automatically get reregistered when the Umbrella module is restarted, provided the deployment key in their mobileconfigAndroid.txt file is active. |
This feature facilitates seamless device registration and ongoing validation while offering the flexibility to deactivate keys when necessary. If any unauthorized devices try to connect, administrators can swiftly deactivate the current deployment key and delete the suspected devices from the dashboard, ensuring a secure and efficient network environment. The devices will not be able to reregister with the now-deactivated deployment key. Administrators can then activate a new deployment key. This allows IT teams to maintain operational continuity while safeguarding against unauthorized access.
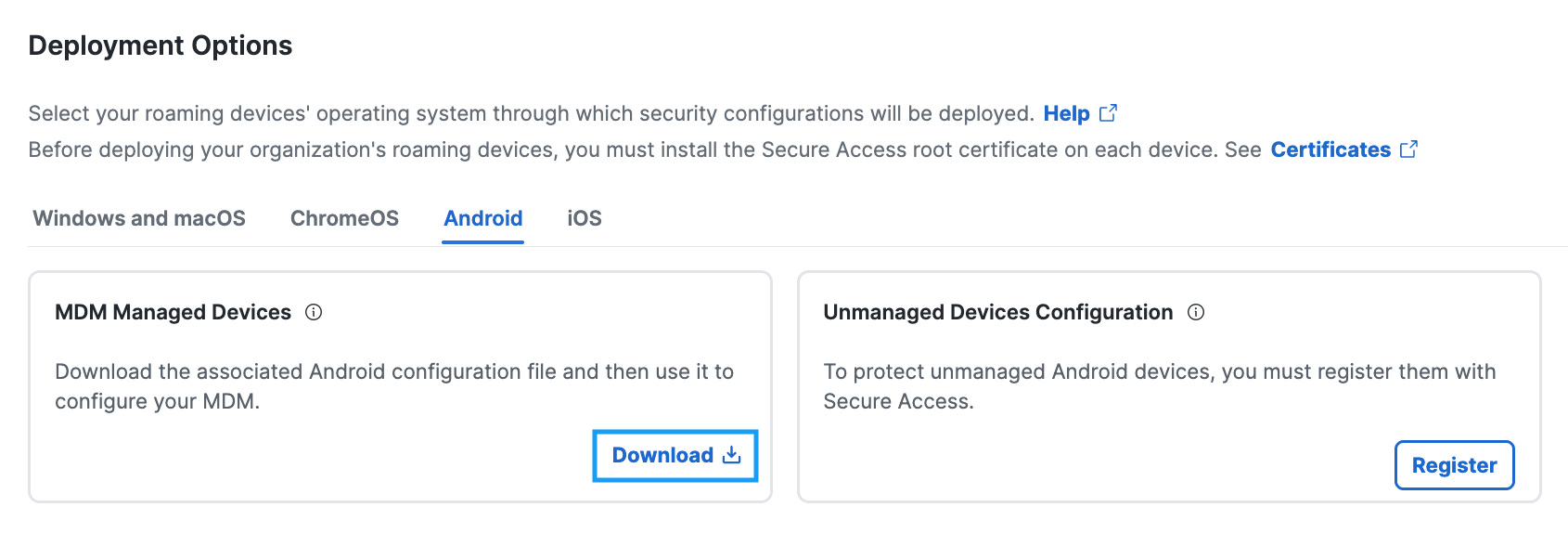
If your Secure Access deployment requires a deployment key, or if your organization has already enabled them, the Android configuration file can only be downloaded when there is an active deployment key (see image below). Then, register your supervised Android device through your Mobile Device Manager (MDM) to Secure Access. For more information, see Android Configuration Download.
Prerequisites for Device Deployment Management
- For the Global deployment, the Deployment key feature is optional. Enable the Deployment Keys feature (Connect > End User Connectivity > Internet Security) if it is disabled.

