Step 2
Procedure
| 1 |
Sign into the Google Admin console. |
||
| 2 |
Navigate to .
|
||
| 3 |
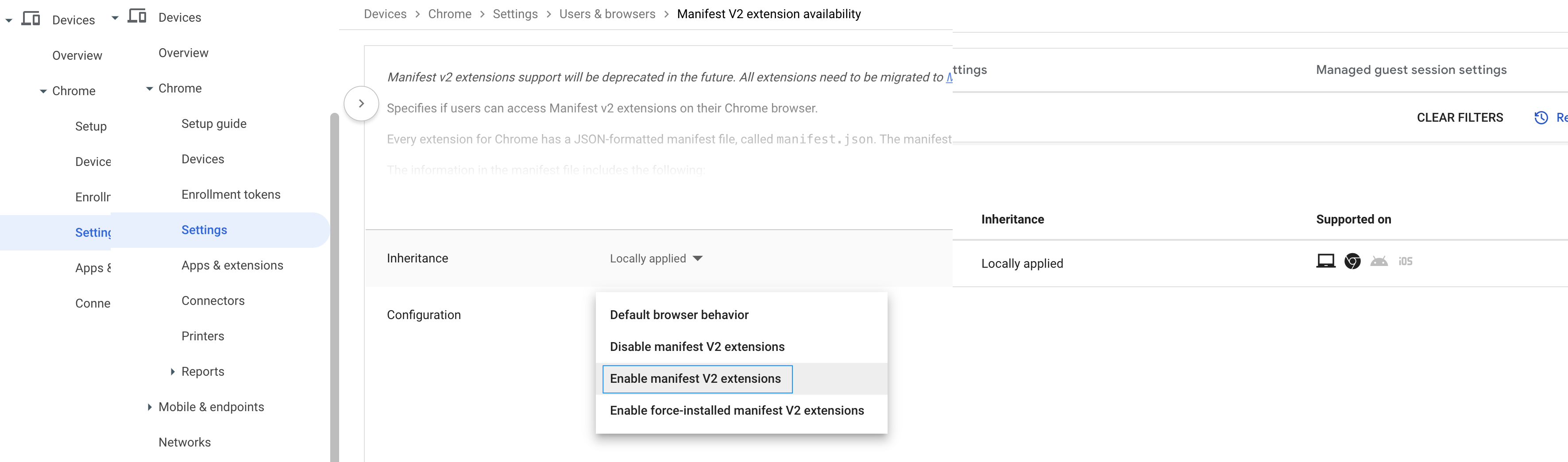
To enable the availability of Manifest V2 extensions, filter the settings for Manifest.

|
||
| 4 |
Select the parent OU on which you want to enable the Manifest V2 extension availability policy. |
||
| 5 |
Click Manifest V2 extension availability. |
||
| 6 |
In the Configuration drop-down list, choose Enable manifest
V2 extensions. |
||
| 7 |
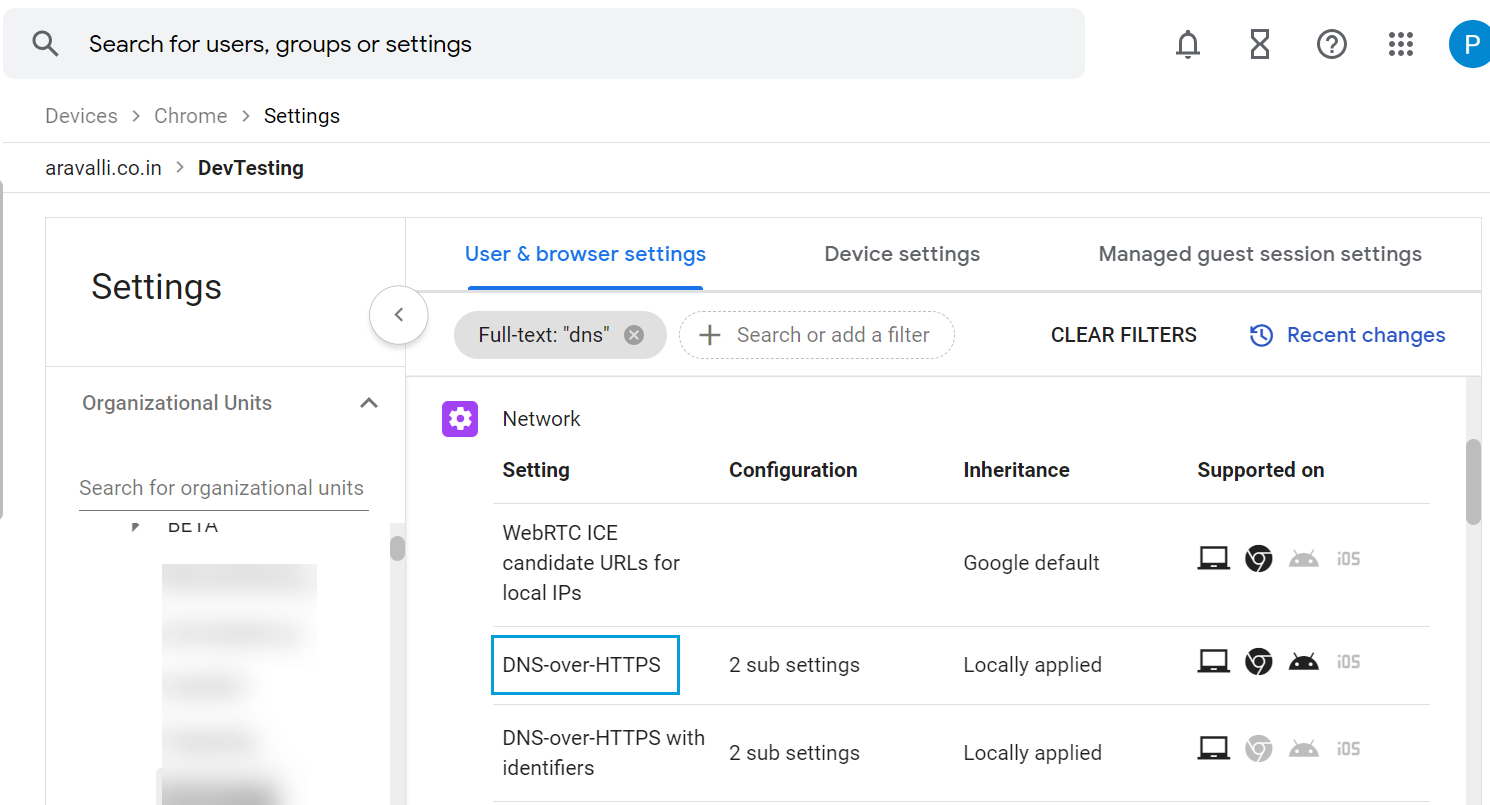
Filter for DNS. |
||
| 8 |
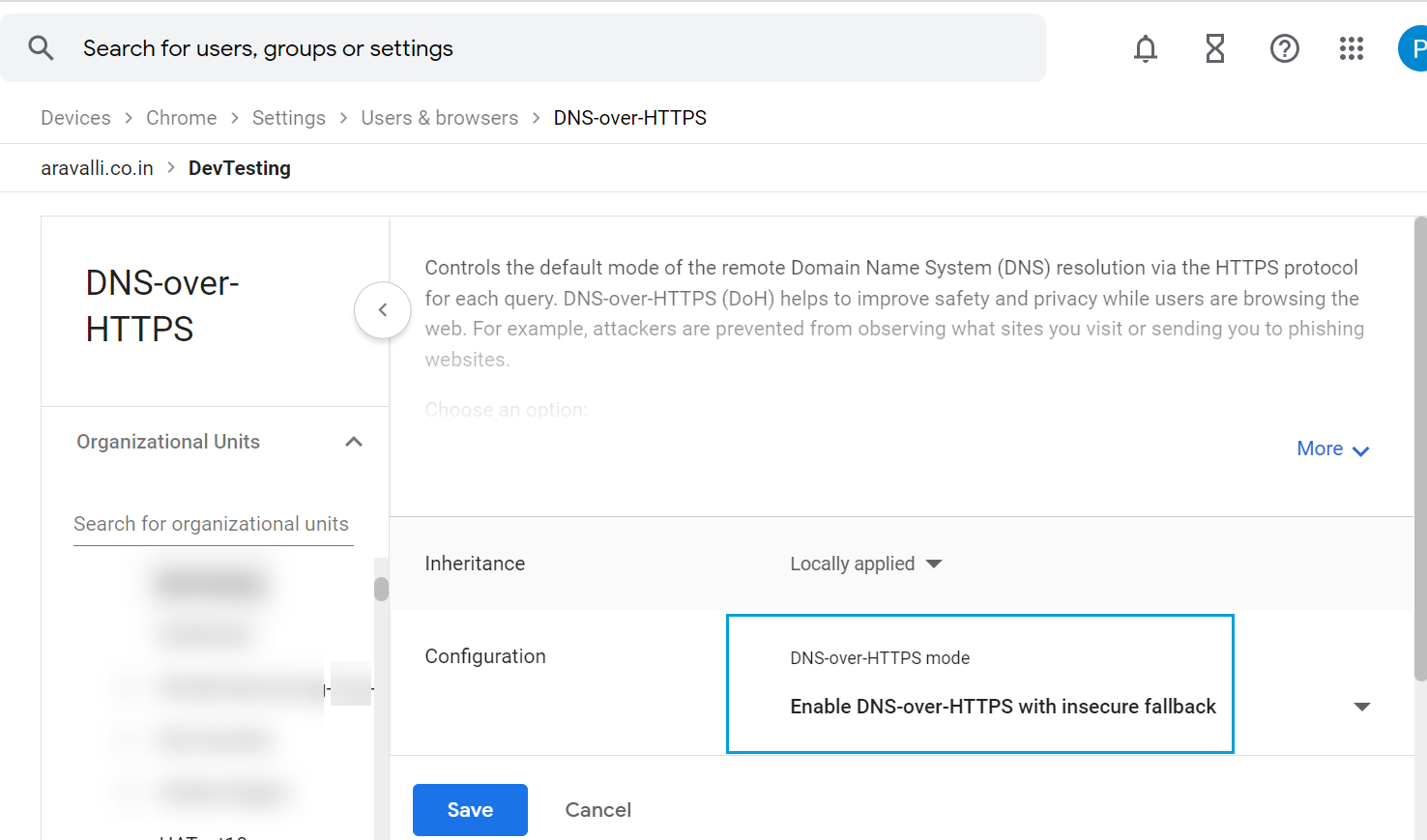
Click DNS-over-HTTPS and configure it to Enable
DNS-over-HTTPS with insecure fallback. |
||
| 9 |
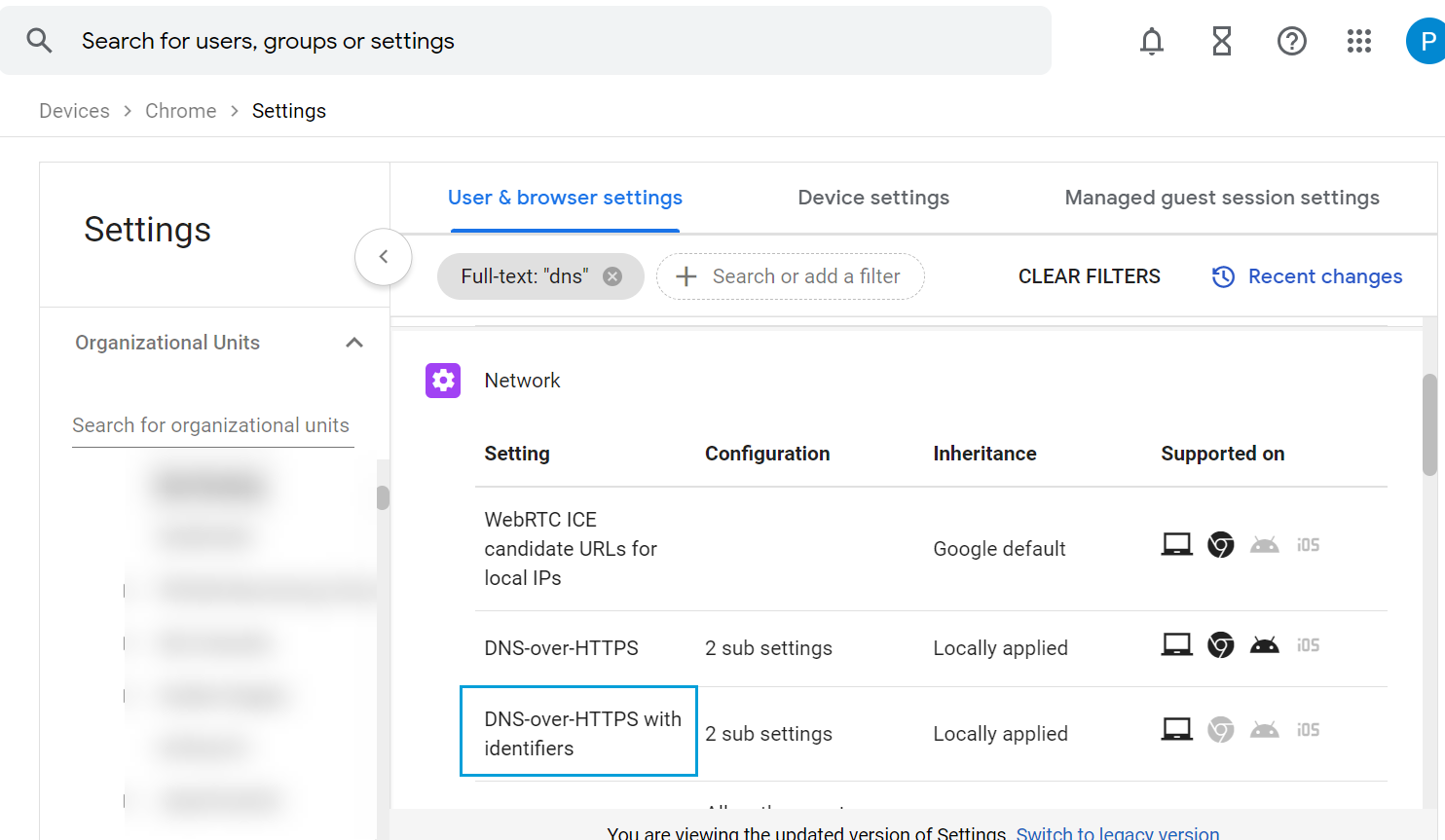
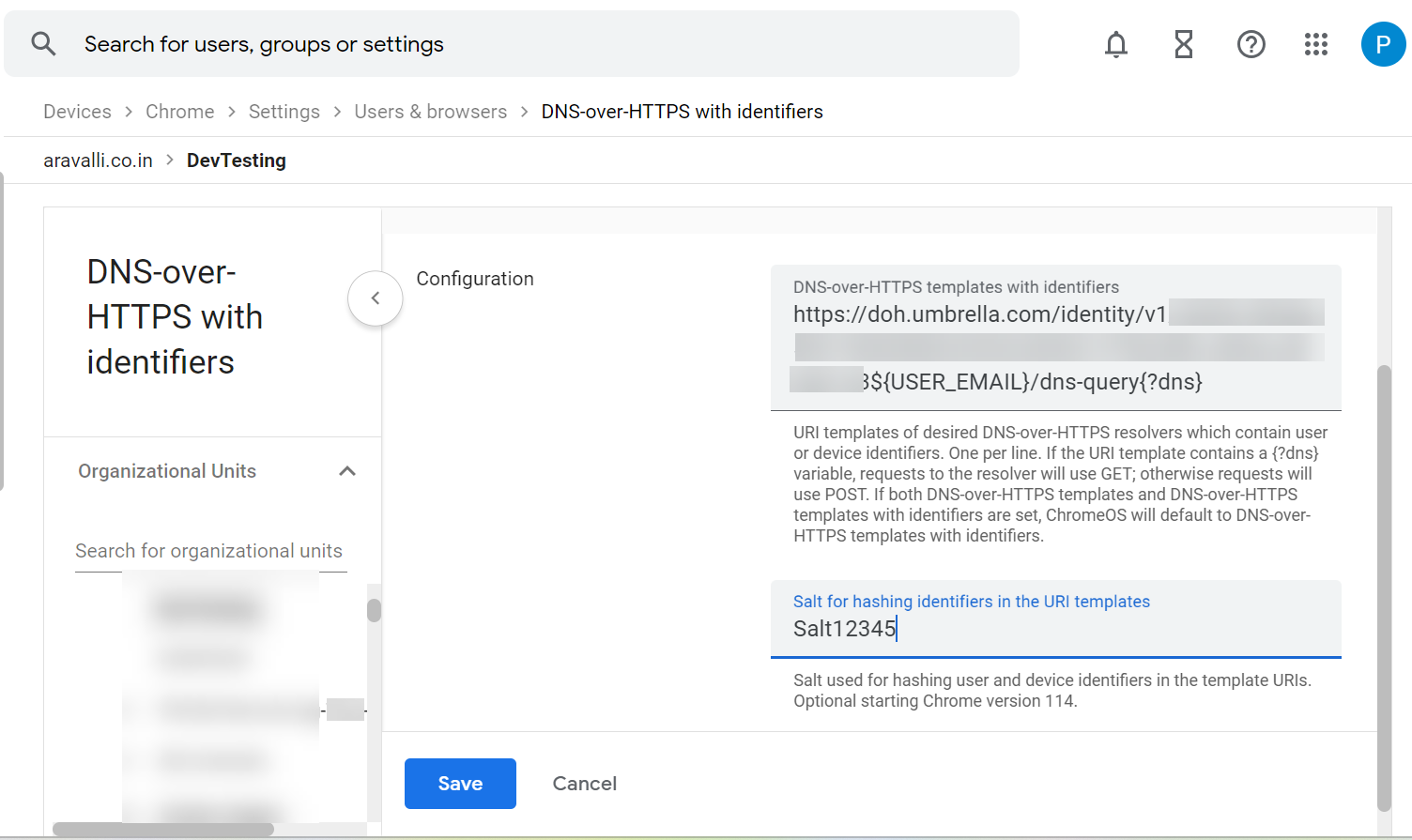
Return to the Users & browser settings page and click
DNS-over-HTTPS with Identifiers. |
||
| 10 |
Enter the URL of the Default DoH template that you copied from Secure Access. |
||
| 11 |
Enter the salt value that you copied from Secure Access. |
||
| 12 |
Click Save. |
||
| 13 |
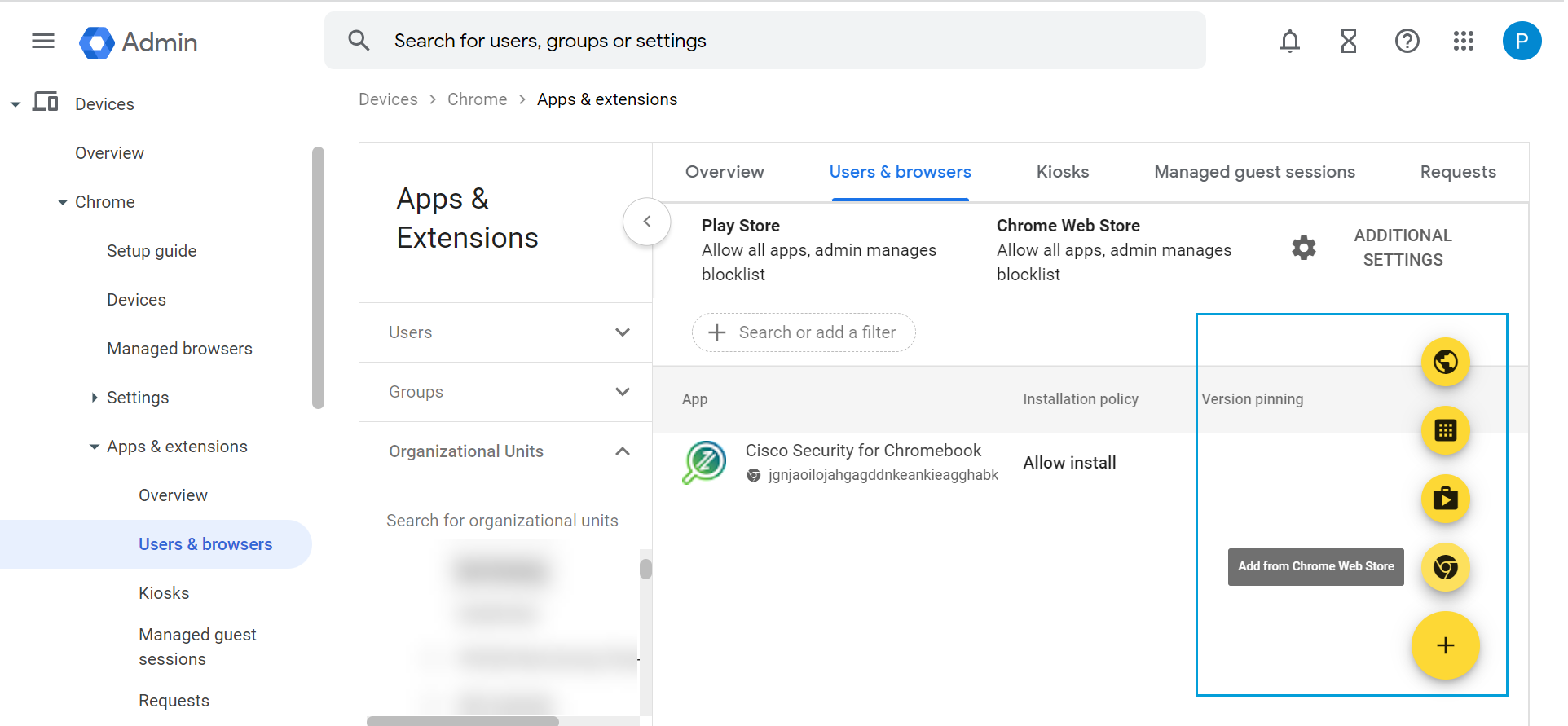
From Apps & Extensions, navigate to . |
||
| 14 |
Expand Organizational Units and choose the OU to which you want to deploy Cisco Security for Chromebook client. |
||
| 15 |
Click + and select Add from Chrome Web Store. |
||
| 16 |
In the Chrome Web Store, navigate to Extensions. |
||
| 17 |
Search for the Cisco Security for Chromebook client extension using the ID jgnjaoilojahgagddnkeankieagghabk.
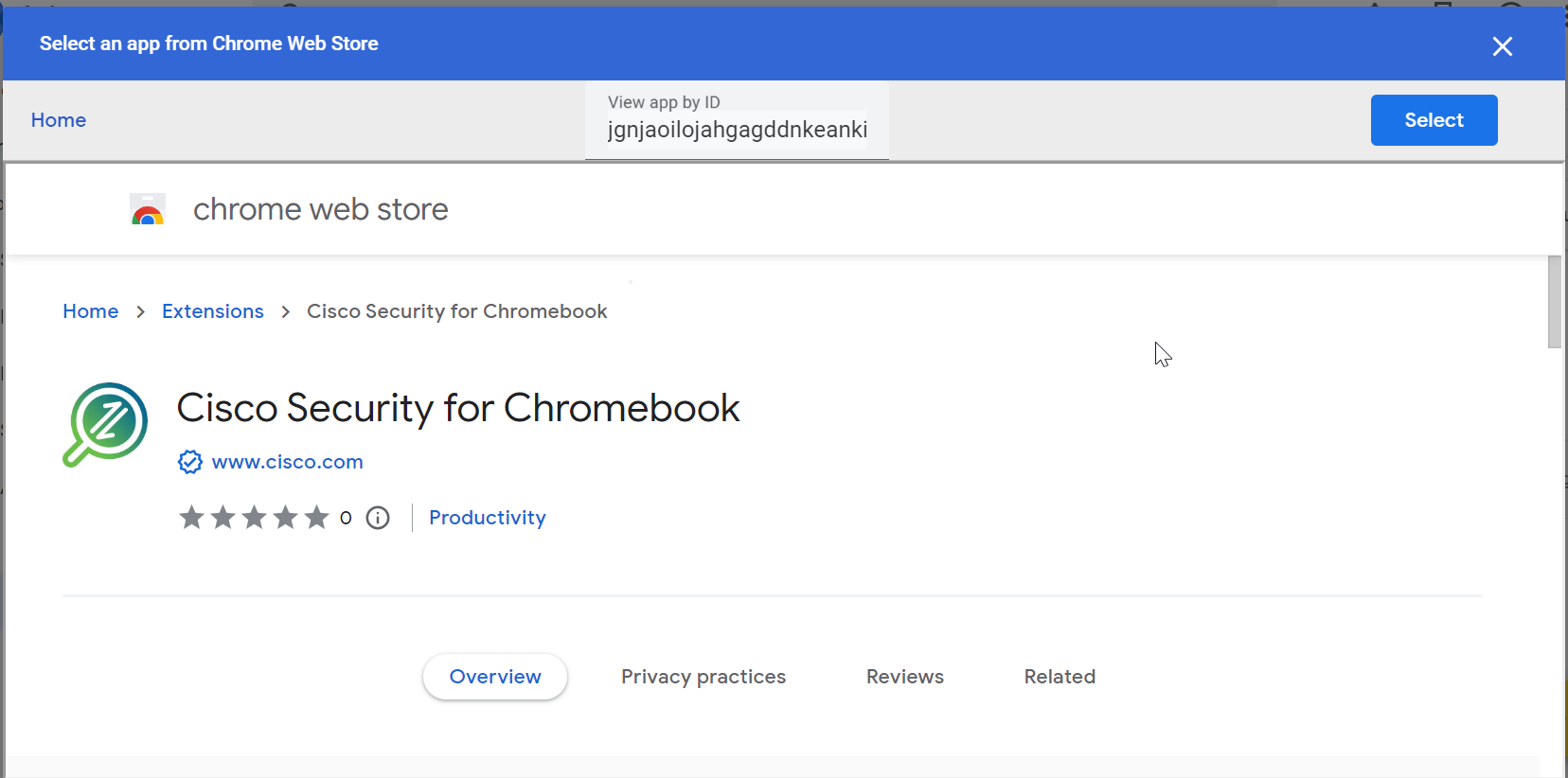
|
||
| 18 |
Click Select. Result: The extension is added to the selected organization unit. |
||
| 19 |
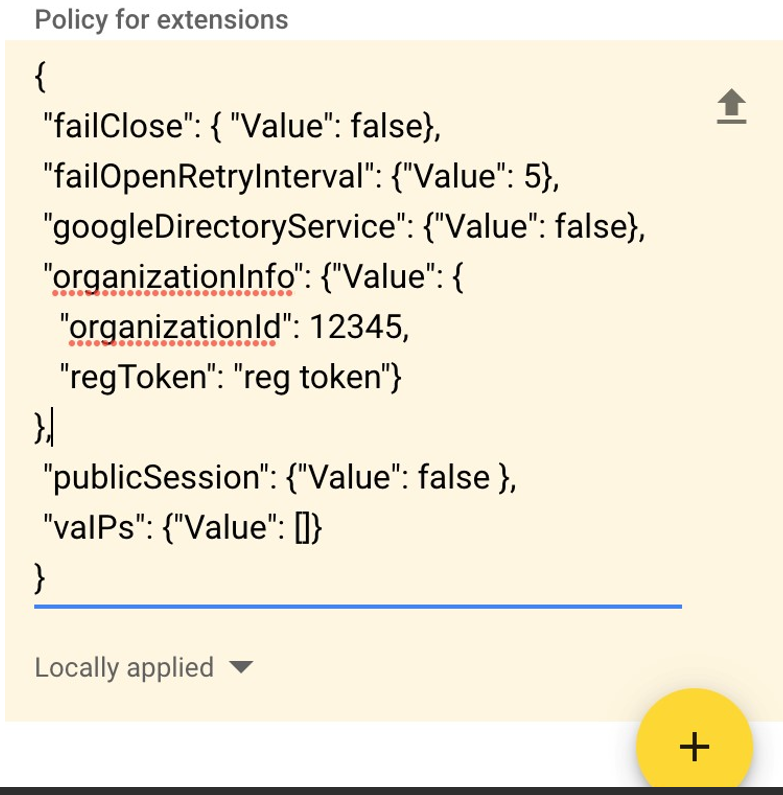
For the JSON file you downloaded, click the Upload link to upload the
file.
|
||
| 20 |
Choose Force install. |
||
| 21 |
Click Save. Result: The Cisco Security for Chromebook client extension is installed. Force install ensures that Chromebook users in the organization unit cannot remove or disable the extension. |
||
| 22 |
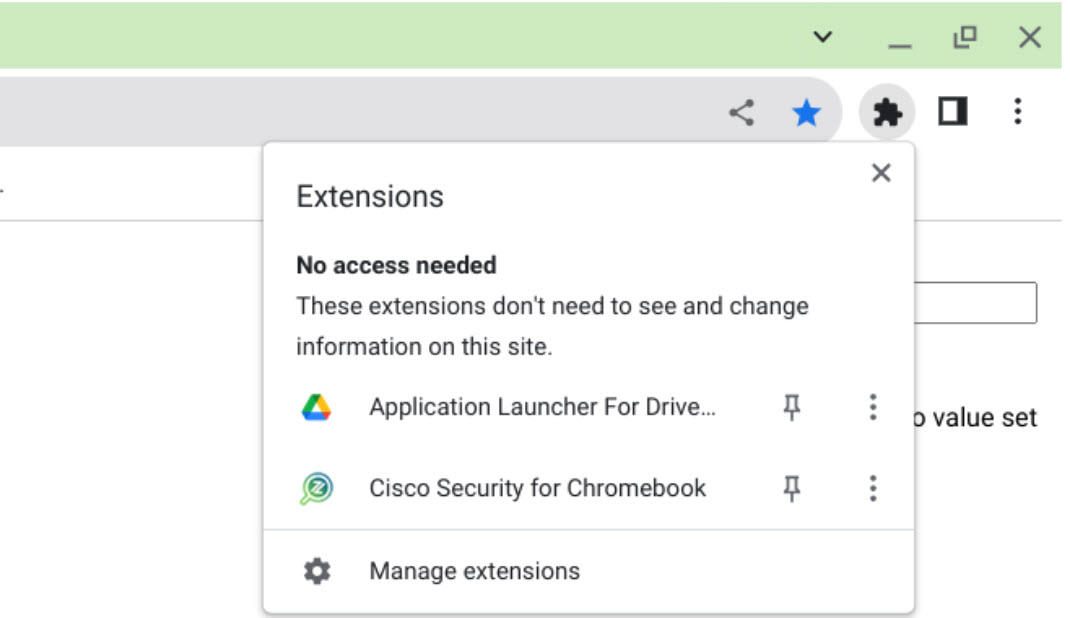
Confirm that Cisco Security for Chromebook client is installed on the Chromebooks and that
the old Umbrella Chromebook Client (app and extension) is blocked. |
||
| 23 |
To verify that a device is being protected by Secure Access, go to <https://policy.test.sse.cisco.com> |
||
| 24 |
A confirmation message displays.
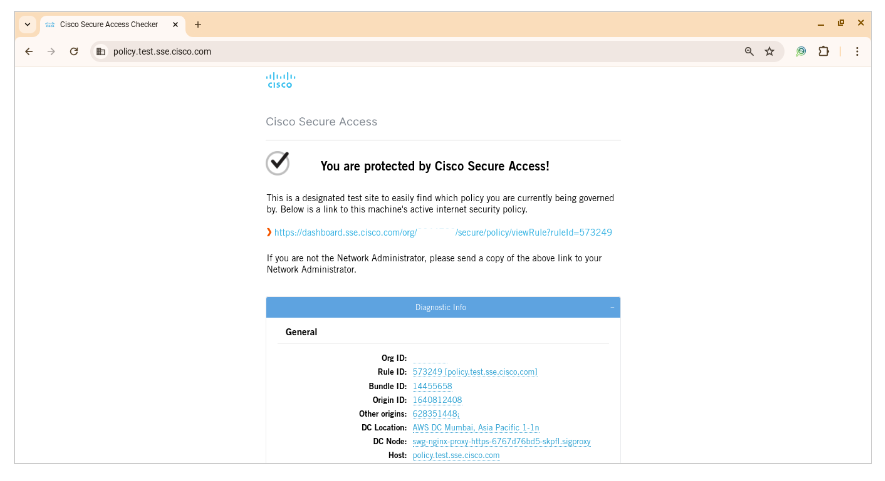
|