Hybrid Private Access Workflow
The Set up hybrid private access workflow shows you how to configure universal Zero Trust
Network Access (ZTNA), in a sequence. Note that you can modify any part of the configuration,
as required.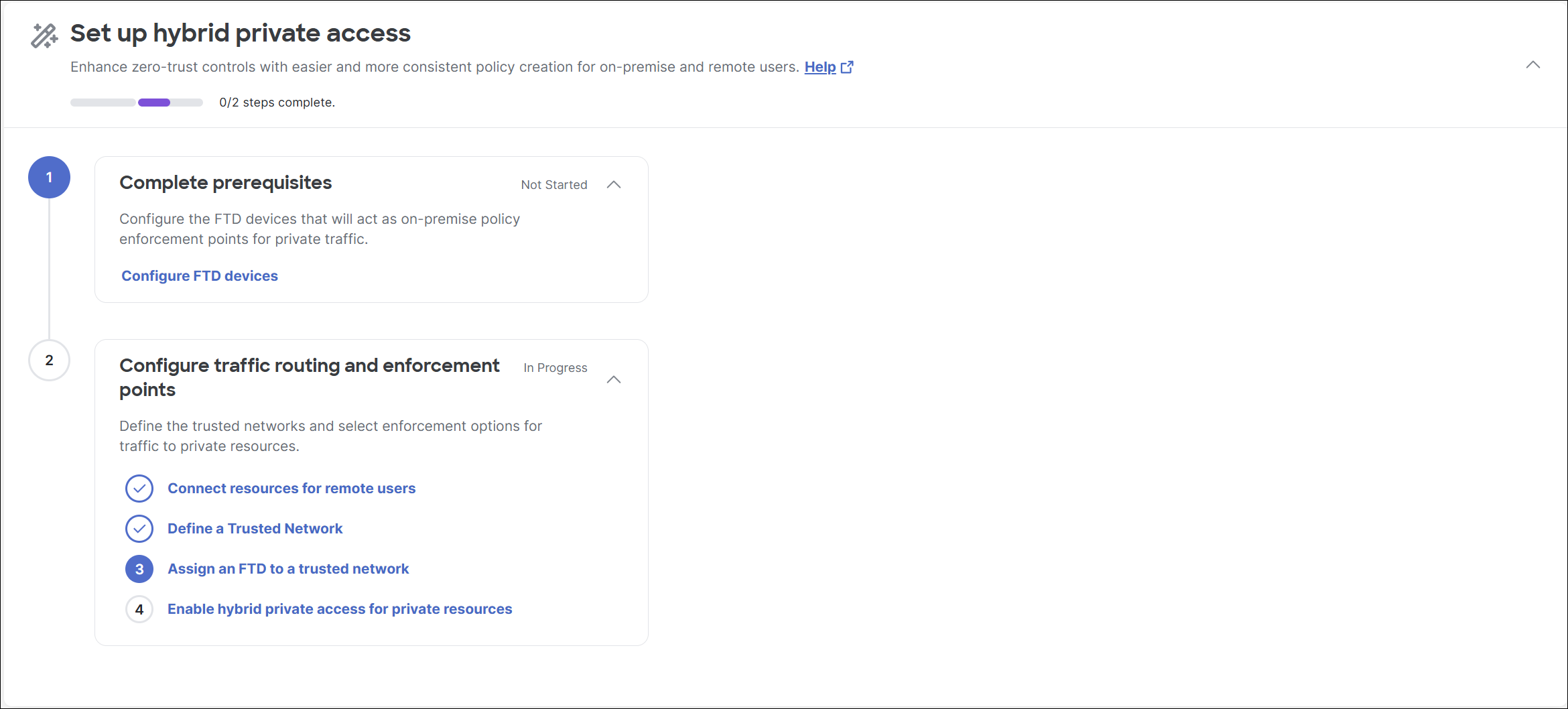
The Set up hybrid private access workflow consists of these broad steps:
- Configure FTD devices: This step guides you through the process of configuring the Firewall Threat Defense devices in Security Cloud Control to enable universal Zero Trust Network Access. After configuration, the Threat Defense devices are displayed in Secure Access under Connect > Network Connections > FTDs, from where you can configure traffic routing and enforcement points.
- Configure traffic routing and enforcement points. This step consists of four tasks:
- Connect resources for remote users: This task guides you through the process of adding resource connector groups or network tunnel groups. A resource connector group supports remote network connections using Zero Trust Network Access to private resources.
- Define a trusted network: This task guides you through the process of adding trusted networks. These networks enable the system to recognize when an endpoint device is connected to a predefined trusted network, allowing the system to enforce security policies and control access to associated private resources.
- Assign an FTD to a trusted network: This task guides you through the process of assigning trusted networks to a Threat Defense device. In turn, the Threat Defense device enforces policies for the private resources associated with the assigned trusted network.
- Enable hybrid private access for private resources: This task guides you through the process of associating private resources with a Threat Defense device to ensure on-premises rule enforcement instead of on-cloud enforcement.
